Bastion Host
Overview
This service creates a single EC2 instance that is meant to serve as a bastion host.
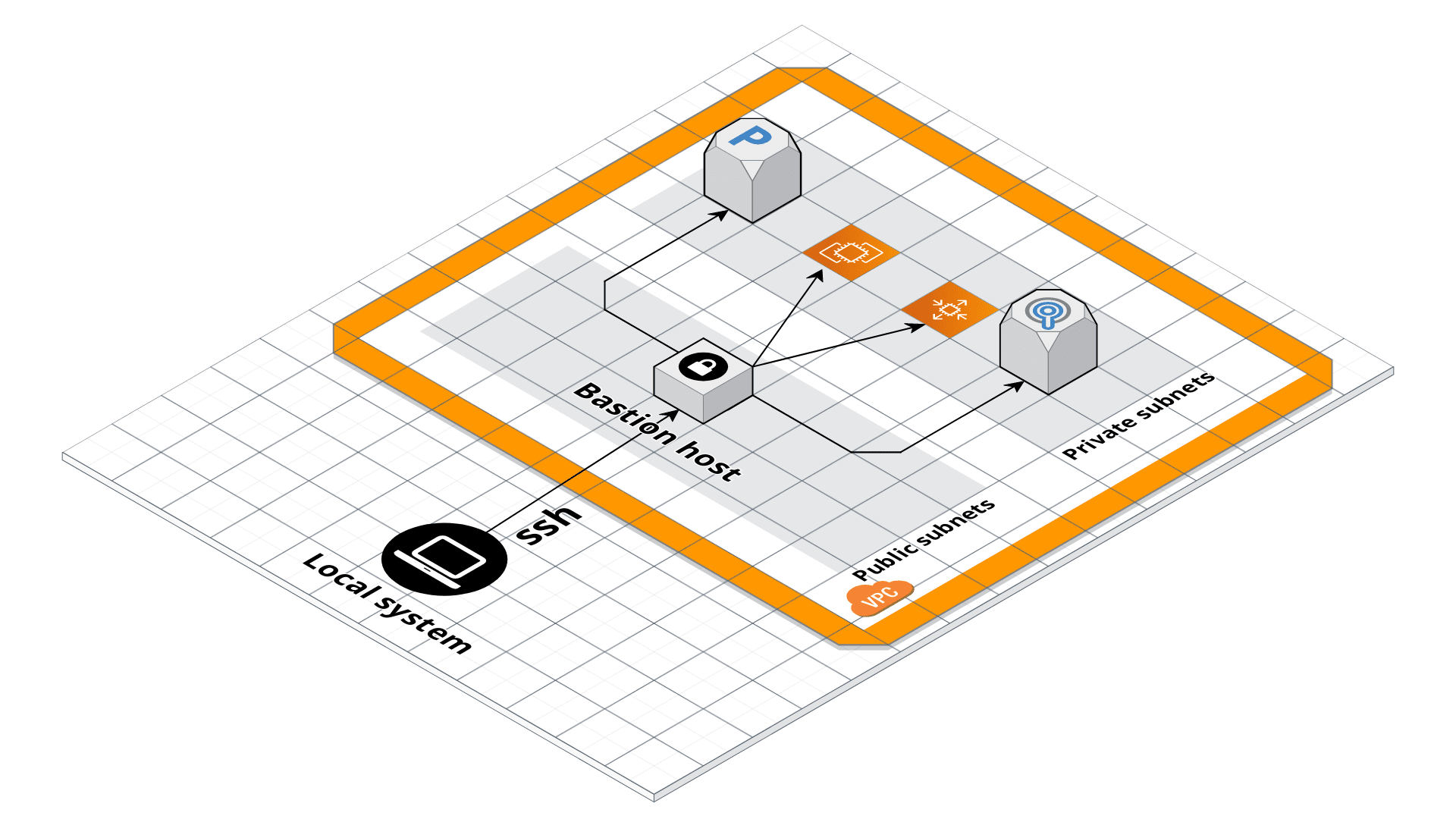 Bastion architecture
Bastion architecture
A bastion host is a security practice where it is the only server exposed to the public. You must connect to it before you can connect to any of the other servers on your network. This way, you minimize the surface area you expose to attackers, and can focus all your efforts on locking down just a single server.
Features
- Build an AMI to run on the bastion host
- Create EC2 instance for the host
- Allocate an Elastic IP Address (EIP) and an associated DNS record
- Create an IAM Role and IAM instance profile
- Create a security group allowing access to the host
- Harden the OS by installing
fail2ban,ntp,auto-update,ip-lockdown, and more - Send all logs and metrics to CloudWatch
- Configure alerts in CloudWatch for CPU, memory, and disk space usage
- Manage SSH access with IAM groups using
ssh-grunt
Learn
note
This repo is a part of the Gruntwork Service Catalog, a collection of reusable, battle-tested, production ready infrastructure code. If you’ve never used the Service Catalog before, make sure to read How to use the Gruntwork Service Catalog!
Core concepts
To understand core concepts like why you should use a bastion host, how to connect to the bastion host, how to use the bastion host as a "jump host" to connect to other instances, port forwarding, and more, see the bastion-host documentation documentation in the terraform-aws-server repo.
The bastion host AMI
The bastion host AMI is defined using the Packer templates bastion-host-ubuntu.json (Packer
< v1.7.0) and bastion-host-ubuntu.pkr.hcl (Packer >= v1.7.0). The template configures the AMI to:
Run the ssh-grunt module so that developers can upload their public SSH keys to IAM and use those SSH keys, along with their IAM user names, to SSH to the bastion host.
Run the auto-update module so that the bastion host installs security updates automatically.
Optionally run the syslog module to automatically rotate and rate limit syslog so that the bastion host doesn’t run out of disk space from large volumes of logs.
Deploy
Non-production deployment (quick start for learning)
If you just want to try this repo out for experimenting and learning, check out the following resources:
- examples/for-learning-and-testing folder: The
examples/for-learning-and-testingfolder contains standalone sample code optimized for learning, experimenting, and testing (but not direct production usage).
Production deployment
If you want to deploy this repo in production, check out the following resources:
- examples/for-production folder: The
examples/for-productionfolder contains sample code optimized for direct usage in production. This is code from the Gruntwork Reference Architecture, and it shows you how we build an end-to-end, integrated tech stack on top of the Gruntwork Service Catalog, configure CI / CD for your apps and infrastructure.
Reference
- Inputs
- Outputs
additional_security_group_ids— A list of optional additional security group ids to assign to the bastion server.
alarms_sns_topic_arn— The ARNs of SNS topics where CloudWatch alarms (e.g., for CPU, memory, and disk space usage) should send notifications.
allow_ssh_from_cidr_list— A list of IP address ranges in CIDR format from which SSH access will be permitted. Attempts to access the bastion host from all other IP addresses will be blocked. This is only used ifallow_ssh_from_cidris true.
ami— The AMI to run on the bastion host. This should be built from the Packer template under bastion-host.json. One of var.ami orami_filtersis required. Set to null if looking up the ami with filters.
ami_filters— Properties on the AMI that can be used to lookup a prebuilt AMI for use with the Bastion Host. You can build the AMI using the Packer template bastion-host.json. Only used if var.ami is null. One of var.ami orami_filtersis required. Set to null if passing the ami ID directly.
base_domain_name_tags— Tags to use to filter the Route 53 Hosted Zones that might match the hosted zone's name (use if you have multiple public hosted zones with the same name)
cloud_init_parts— Cloud init scripts to run on the bastion host while it boots. See the part blocks inhttps://www.terraform.io/docs/providers/template/d/cloudinit_config.html for syntax.
cloudwatch_log_group_kms_key_id— The ID (ARN, alias ARN, AWS ID) of a customer managed KMS Key to use for encrypting log data.
cloudwatch_log_group_retention_in_days— The number of days to retain log events in the log group. Refer tohttps://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/cloudwatch_log_group#retention_in_daysfor all the valid values. When null, the log events are retained forever.
cloudwatch_log_group_tags— Tags to apply on the CloudWatch Log Group, encoded as a map where the keys are tag keys and values are tag values.
create_dns_record— Set to true to create a DNS record in Route53 pointing to the bastion. If true, be sure to setdomain_name.
default_user— The default OS user for the Bastion Host AMI. For AWS Ubuntu AMIs, which is what the Packer template in bastion-host.json uses, the default OS user is 'ubuntu'.
domain_name— The apex domain of the hostname for the bastion server (e.g., example.com). The complete hostname for the bastion server will bename.var.domain_name(e.g., bastion.example.com). Only used ifcreate_dns_recordis true.
enable_cloudwatch_alarms— Set to true to enable several basic CloudWatch alarms around CPU usage, memory usage, and disk space usage. If set to true, make sure to specify SNS topics to send notifications to usingalarms_sns_topic_arn.
enable_cloudwatch_log_aggregation— Set to true to send logs to CloudWatch. This is useful in combination with https://github.com/gruntwork-io/terraform-aws-monitoring/tree/master/modules/logs/cloudwatch-log-aggregation-scripts to do log aggregation in CloudWatch.
enable_cloudwatch_metrics— Set to true to add IAM permissions to send custom metrics to CloudWatch. This is useful in combination with https://github.com/gruntwork-io/terraform-aws-monitoring/tree/master/modules/agents/cloudwatch-agent to get memory and disk metrics in CloudWatch for your Bastion host.
enable_fail2ban— Enable fail2ban to block brute force log in attempts. Defaults to true.
enable_ip_lockdown— Enable ip-lockdown to block access to the instance metadata. Defaults to true.
enable_ssh_grunt— Set to true to add IAM permissions for ssh-grunt (https://github.com/gruntwork-io/terraform-aws-security/tree/master/modules/ssh-grunt), which will allow you to manage SSH access via IAM groups.
external_account_ssh_grunt_role_arn— If you are using ssh-grunt and your IAM users / groups are defined in a separate AWS account, you can use this variable to specify the ARN of an IAM role that ssh-grunt can assume to retrieve IAM group and public SSH key info from that account. To omit this variable, set it to an empty string (do NOT use null, or Terraform will complain).
instance_type— The type of instance to run for the bastion host
keypair_name— The name of a Key Pair that can be used to SSH to this instance.
name— The name of the bastion host and the other resources created by these templates
should_create_cloudwatch_log_group— When true, precreate the CloudWatch Log Group to use for log aggregation from the EC2 instances. This is useful if you wish to customize the CloudWatch Log Group with various settings such as retention periods and KMS encryption. When false, the CloudWatch agent will automatically create a basic log group to use.
ssh_grunt_iam_group— If you are using ssh-grunt, this is the name of the IAM group from which users will be allowed to SSH to this Bastion Host. This value is only used ifenable_ssh_grunt=true.
ssh_grunt_iam_group_sudo— If you are using ssh-grunt, this is the name of the IAM group from which users will be allowed to SSH to this Bastion Host with sudo permissions. This value is only used ifenable_ssh_grunt=true.
tenancy— The tenancy of this server. Must be one of: default, dedicated, or host.
vpc_id— The ID of the VPC in which to deploy the bastion.
bastion_host_iam_role_arn— The ARN of the bastion host's IAM role.
bastion_host_instance_id— The EC2 instance ID of the bastion host.
bastion_host_private_ip— The private IP address of the bastion host.
bastion_host_public_ip— The public IP address of the bastion host.
bastion_host_security_group_id— The ID of the bastion hosts's security group.
dns_name— The fully qualified name of the bastion host.